TechCrunch Disrupt (TCD) 2019 in San Francisco lands on the same week as the one-year anniversary of Cisco’s acquisition of Duo Security, the leading multi-factor authentication (MFA) and Zero Trust for the Workforce provider. It was only fitting that Dug Song, the co-founder and general manager of Duo, took the stage at TCD to speak to the crowd about building secure startups.
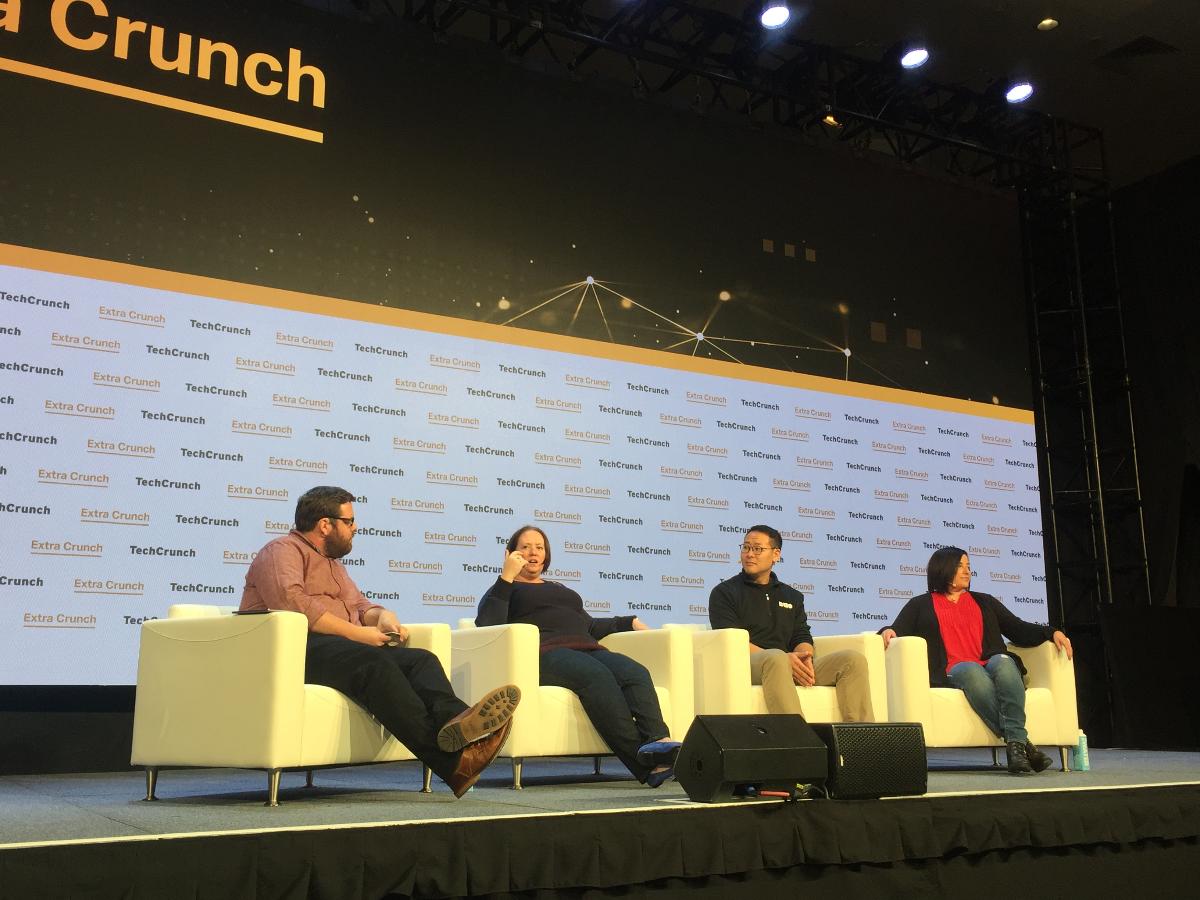
Song spoke at the TCD session, “How to build a secure startup without slowing growth." The panel was a fitting discussion for the Silicon Valley startup and enterprise crowd who were seeking ways to grow while still remaining safe.
Here are six tips from Dug for startups to stay secure.
1. The 3 areas for startups to consider risk
“The three areas to consider are corporate security, application security, and production security,” says Song, “The reality is that most startups don’t think about security, but they must consider risk. It’s not just strategic, but it’s also about keeping your operations safe.
2. Put yourself in your customer’s shoes
Security isn’t just about your organization—it’s about your customers and partners as well. Consider the effects of a data leak from another’s perspective.
“As soon as you start carrying anyone else’s data, you have put yourself in the shoes of the people with the data you have to protect,” says Song.
3. Security needs to be the default
Installing security measures in a startup shouldn’t mean putting the brake on things. Song says if you do it right, the safest path should also be the easiest one.
“The security team should be creating better, safer choices, which are also simple for people to use,” says Song. “Security should be built-in rather than bolted on. There are a lot of good choices out there of security by default. That’s one of the advantages as a small company—you don’t have as much legacy, so you can start using security from the beginning.
4. Complexity is the real enemy of security
Simplify, simplify, simplify. Song recommends using just a few programming languages rather than a couple dozen to keep things as minimal as possible.
“Reduce and simplify,” says Song. “You can put things behind single sign on, so that users can have one point of control. Get the basics right, and then you can work on detection and response.”
5. Security requires diversity
Attackers are coming from all angles, which means that security teams also need multiple points of view.
“It’s not just network controls or gaining access, attackers are going after users in very crafty ways,” says Song. “There needs to be a number of different skillsets so that security teams are instructed from all directions. It takes all kinds. Not just the rockstars and gurus— very often the mundane aspects of security get overlooked. Everyone brings a different perspective.”
6. Security requires a cultural commitment
It’s time to take the blaming and shaming out of security. Instead of victimizing the first person to click on a bad link, you can commend them for being the first to report it.
“Security requires a cultural commitment,” says Song, “where people are not blamed for clicking on the link. Actually, you can tell them they were the first to report that, which is a good thing. This also helps with reducing the amount of time to detect or detain.”
Cisco and Duo
Cisco’s acquisition of Duo was one of the most significant merger and acquisition events in cybersecurity within the last year. In that time, Duo has helped drive diversification to a recurring, subscription-based revenue. Duo is continually helping Cisco’s security evolution, jointly protecting organizations against data breach by making security easy and effective.
The security perimeter is constantly expanding. With so many devices and applications being used, access can happen anywhere and from any device. Cisco Zero Trust Security now provides secure access for the workforce, workloads, and the workplace.
A zero-trust security approach assumes “zero trust” when someone or something requests access to work assets. Cisco Zero Trust helps prevent unauthorized access, contain breaches, and reduce the risk of lateral movement. With this framework, organizations can easily verify a user’s trustworthiness before granting access to them. Cisco Zero Trust does this by using three different products; Software-Defined (SD) Access, Tetration, and Duo. SD Access helps secure and segment access for users, apps, and devices across the network, Tetration secures access across the multi-cloud and data center, and Duo secures user access to applications from any device or location.
To learn more about how to secure your company from all angles, check out Cisco Zero Trust Security.
###
We welcome the re-use, republication, and distribution of "The Network" content. Please credit us with the following information: Used with the permission of http://thenetwork.cisco.com/.




