
Phishing may feel like a recent term but the attack type is a decades-old scam
Phishing for information is a socially-based attack that has deep roots on the Internet. The quirky spelling, with a PH instead of an F, is a not so subtle nod to a hacker class called phreaks.

After nearly 36 years since it was first referenced, and nearly 30 years since the first primitive forms of the attack started in chatrooms, phishing is still one of the largest threats on the internet.
Let's dive into Phishing's history, evolution and predictions for the future...
The Evolution of Phishing

Phishing Lore
At the INTEREX conference, Jerry Felix and Chris Hauck present a paper called “System Security: A Hacker’s Perspective” and describes an attack where a third-party can imitate a trusted service. Copies of this paper are next to non-existent today, making the presentation a bit of phishing lore in security circles.
What the AOHell?
A Visual Basic tool called AOHell is released by a hacker named Koceilah Rekouche, known as “Da Chronic” who writes that it is basically “used to annoy others, get free service, and other things.” The tool includes a credit card number generator, as well as email and Instant Message bombers. [1][3]


If you ask nicely…
AOHell implements a function called CC/PW Fisher which would message a victim and attempt to get them to share sensitive information. One message states: “Hi, this is AOL customer service. Due to a problem with our records, we need you to reply to this message with your current password in order to avoid being disconnected.” [3]
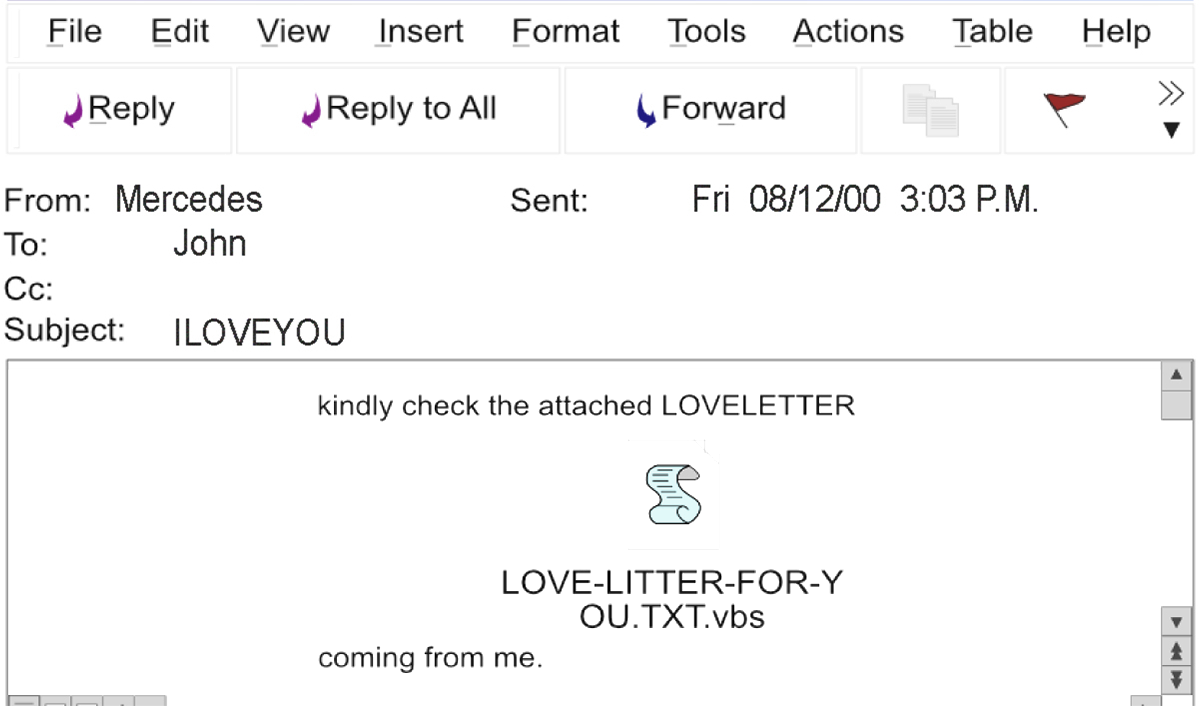
Did you get the love bug?
The internet is introduced to emails with the subject line “ILOVEYOU” and being asked to open the attached love letter. It is a virus, and the Love Bug quickly spreads to millions of computers across the globe.

All that glitters is not gold
The world first learns of phishing in a major way, as the first known attempt at phishing a payment system happens. Users of the e-gold system, which was a digital gold currency operated by Gold & Silver Reserve, are phished with emails warning about how e-gold is going out of business. Users are directed to clone websites and scammed out of their login and password information. [5]
APWG
The Anti-Phishing Working Group (APWG) is founded.
The first known phishing attack against a retail bank is reported by the financial magazine The Banker in their September issue.


Where there’s profit, there’s a business
The criminal economy fully embraces phishing, and specialized roles are carved out to support those taking part. There are developers, list creators, and programmers who write software used for bulk sending of emails. A thriving credential trading and cash-out market emerged. [6]
Criminal Economic Supply Chains
The Russian Business Network (RBN) makes headlines as the network responsible for hosting 50% of all the groups running phishing campaigns the previous year. According to a report from VeriSign at the time, a phishing collective known as Rock Group used the RBN to phish nearly $150 million from banks in 2005. [8]
Proactive Phishing Protection
According to Gartner, between May 2004 and May 2005, roughly 1.2 million U.S. computer users suffered phishing losses valued at $929 million. Banks started implementing phishing protections.


Plenty of Phish in myspace
Phishing groups start targeting social media, including a massive campaign aimed at users of MySpace.com, which was at the time one of the world’s largest social platforms. [9]
Making the News
Phishing groups leverage the headlines related to a recent weather disaster in January of this year. Dubbed the Storm Worm, the malware spread by these phishing attacks (which often came attached to emails using various newsworthy subject lines) accounted for about 8 percent of the malware infections globally. Here are some of the subject lines used for these attacks:
- 230 Dead as Storm Batters Europe. (The subject line where the malware got its name)
- A Killer at 11, He's Free at 21 to Kill Again!
- U.S. Secretary of State Condoleezza Rice Kicks German Chancellor Angela Merkel
- Venezuelan Leader: "Let's the War Begin"
- FBI vs. Facebook
- USA Occupies Iran


Courts get involved in liability
An employee at Experi-Metal opens a phishing email with a link to a website purporting to be a Comerica Business Connect Customer Form. In all, the phishing attack results in $1.9 million in fraudulent transfers, and the courts rules that Comercia Bank was liable for the $560,000 that could not be recovered, as they should have realized the transfers were fraudulent. [10]
Even security companies get hacked.
Alongside a surge of phishing attacks aimed at Gmail accounts, internal staff at RSA are successfully phished, resulting in the master keys for all RSA SecureID tokens being compromised. The stolen keys were then used to target US defense suppliers. [11]


Cryptolocker
A new attack where system files (or the system itself) are locked and held hostage for a payoff appears: Ransomware.
Spread via phishing and compromised websites, Cryptolocker ransomware hits the web. The attack spreads principally by mimicking tracking info for popular shipping providers. More than 34,000 machines are infected, and Ransomware becomes a mainstay.
Bringing in the Boss
Phishing attacks built on emails impersonating a business's senior executive got their own moniker: Business Email Compromise, or BEC attacks. They become a common criminal tactic in the years ahead.


Phishing jumps on the hopeful.
Attacks start to hook people with the false hope of winning something. trending towards online lottery and prizes Criminals looking to cash-in on the World Cup start sending phishing emails that claim the recipient has won tickets to the event. The victim is directed to a website and prompted to release their personal information to enter the lottery. [20]
Phishing hits critical infrastructure
A phishing attack against Colonial Pipeline ultimately leads to a ransomware incident and the of the largest critical infrastructure attacks on US soil. The company transports 100 million gallons of fuel each day, and is the primary source of gasoline, diesel, and jet fuel for cities across the East Coast. [21]


The future of phishing is going to look much like it does today, but with more of an obvious strategy. You will see more BEC like attacks, and phishing attacks focused on supply chains and third-party vendors, which can then be leveraged on attacks on these vendor's customers. Another example would be targeting companies based on the likelihood of available funds - think cyber security insurance companies whose customers are insured and likely to pay.
Phishing in the future will also focus on personal narrative, and on current events. We see that today, but as the world gets more divisive, criminals will look to take advantage.



