By Mauricio Sanchez, Dell’Oro Group
Since being coined in mid-2019, Secure Access Service Edge (SASE) has become a hot topic in the networking and security community. The number of technology vendors touting SASE has grown from a handful to over 30. Moreover, services providers are quickly embracing and marketing a new entrée of network and security services under the SASE banner. With the COVID pandemic driving the growth in remote work and the acceleration of digitalization efforts – namely, the shift towards a modern, Internet-based application infrastructure – the environment has been ripe for SASE to flourish.
However, there’s still a significant amount of confusion surrounding SASE. We see, surprisingly, a considerable amount of debate on whether SASE is a network or security solution. Once over this hump, the discussion then turns to implementation and whether SASE is a framework or a product. In this blog, we’d like to clear up these two questions showing how SASE is not only a network and security solution but also a framework and product.
Yes, SASE is Both a Network and Security Solution
We define SASE as a service-centric, cloud-based solution that provides network connectivity and enforces security between users, devices, and applications by using a combination of hardware, software, and centrally-controlled Internet-based networks with built-in networking and security-processing capabilities. It addresses the shortcomings of the legacy hub-and-spoke architecture and improves on recent solutions–in particular, SD-WAN and cloud-based SWGs (which recently started to be known as Secure Service Edge (SSE) solutions)–by bringing networking and security into a unified service that increases network scalability, agility, and security.
While some in the community characterize SASE as primarily a security solution, we believe this view is too limiting and unfairly undercuts networking technologies’ role. The shift toward cloud-based network architectures that rely on general-purpose Internet connections and multi-cloud deployments does not simplify enterprise IT networking. On the contrary, it makes it more complicated. Hence, we believe that WAN technologies that help manage the increased complexity of modern networks, like SD-WAN, are fundamental to the SASE equation.
Yes, SASE is Both a Framework and a Product
With SASE rooted in SD-WAN and cloud-based SWG precursors, it shares the same architectural underpinnings and has similar components as those technologies. SASE consists of five components: the network, control plane software, functions, endpoints, and appliances (Figure 1).
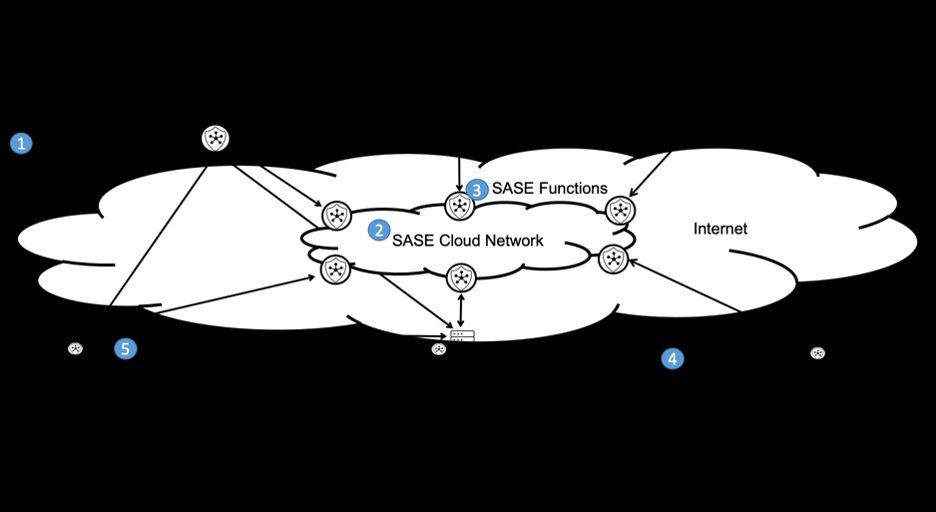
Figure 1: SASE Architecture and Five Core Components (New Option 2)
When implementing a SASE architecture, technology vendors are taking a framework or product approach. Some vendors are even embracing both in the name of customer choice.
In the framework approach, which we call a disaggregated SASE, separate network and security technologies have been integrated into a complete SASE deployment. The network and security technologies may come from the same or different SASE vendors. Usually, disaggregated implementations consist of multiple policy repositories–one for each network or security service. This distinction becomes important when compared with the product approach.
In the product approach, which we call a unified SASE, all network and security technologies are implemented by a vendor as a single, tightly integrated product platform with just one policy repository spanning network and security policy. Moreover, all five key SASE components typically are offered and required to be obtained from the same vendor.
Beyond the near-term convergence of networking and security in SASE, longer-term we see the next generation of SASE extending the cloud edge to the enterprise edge since there is a clear need to deliver a consistent experience with seamless enforcement and control across cloud and on-prem.
Neither approach to SASE is a “one size fits all” since each has advantages and disadvantages. For example, the multiple policy repositories in disaggregated SASE–because often the deployment consists of numerous products from various vendors– may require manual and sometimes difficult policy reconciliation by administrators that the unified SASE avoids due to its more monolithic implementation. However, the more monolithic implementation of unified SASE may make it more difficult to integrate third-party technologies. Conversely, in disaggregated SASE, it’s generally more straightforward to integrate additional third-party by virtue of its disaggregated implementation.
We believe both forms of SASE will coexist in the market due to the differences in enterprise IT teams. Enterprises with specialized networking and IT teams prefer the multi-vendor, disaggregated SASE approach. This facilitates a best-of-breed SASE deployment that consists of the network and security IT teams’ preferred technology vendors. On the other hand, enterprises that lack specialized networking and security IT teams tend to accept single-vendor, unified implementations. The greater simplicity of the unified implementation and only needing to deal with a single vendor, rather than multiple vendors, holds great appeal.
We see the co-existence of both forms in our tracking of the SASE vendor landscape. While disaggregated SASE revenue was over 10x larger than the unified SASE for full-year 2021, unified SASE experienced a more robust year-over-year (Y/Y) growth of 48% versus the 37% Y/Y of disaggregated SASE. In our 5-year forecast, we expect unified SASE growth to remain stronger over the forecast horizon than disaggregated SASE and by 2026 rise to nearly $3 B, which will represent approximately a quarter of the total SASE opportunity.
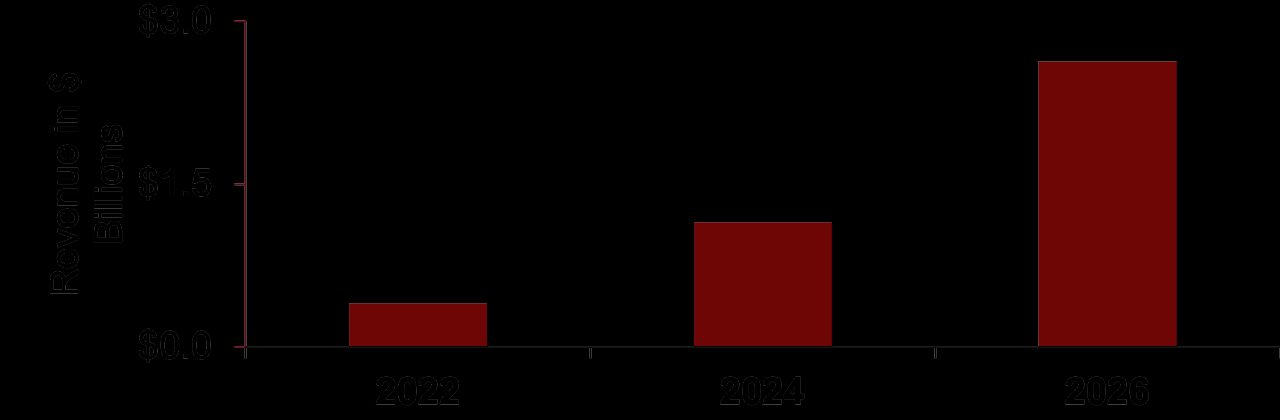
Figure 2: Unified SASE Forecast
The bottom line is that SASE is not only a network and security solution, but also a framework and a product.
###