Part of the job at Cisco® Talos® is not only to track current cyber threats but also predict ones that might crop up in the future. For Martin Lee, technical lead of security research within Talos, that means thinking about tomorrow’s technologies as well as tomorrow’s threats.
And perhaps one of the most tantalizing of tomorrow’s technologies is a quantum computer—a machine that could calculate almost infinite possibilities simultaneously. Here, Lee explains what such capabilities would be mean for the encryption that keeps our digital messages safe.
Q. How does quantum computing differ from today’s computers?
A. In the current architecture of a CPU, we have bits that are either one or zero. In a quantum computer, instead of bits we have qubits that exist in both states—one and zero—and everything in between, at the same time.
So, when we do calculations, we can have all possible solutions to a problem being considered at once. The key thing is it can be much, much faster than current architectures. Also, it means we can do certain calculations which just are not practical using current computers.
Today, this is mostly theoretical: quantum computing is probably at the level of complexity that the silicon chip was in the late 60s or early 70s. But from a security point of view, we can very clearly see at least one of the implications.
Q. What is it? How would quantum computing threaten current enterprise security?
A. It all comes down to multiplication. Any number can be represented as multiples of prime numbers. But if you have a very large number and you want to identify its primes, it is very difficult to do. It takes an unfeasible amount of time using current computing architectures.
In quantum computers, however, we know there is a way we can calculate this very easily, very fast. So, we can identify the prime numbers in large numbers easily. There are all sorts of applications for this which are going to bring all sorts of advantages to our lives.
But our current encryption algorithms depend on the fact that it is difficult to calculate the primes of large numbers. When somebody creates a quantum computer of a suitable size, they will be able to crack many of our current secure encryption algorithms very easily.
This is going to be a massive change for the way we keep data secure through encryption.
Q. How close are we to quantum computing being a real threat for encryption?
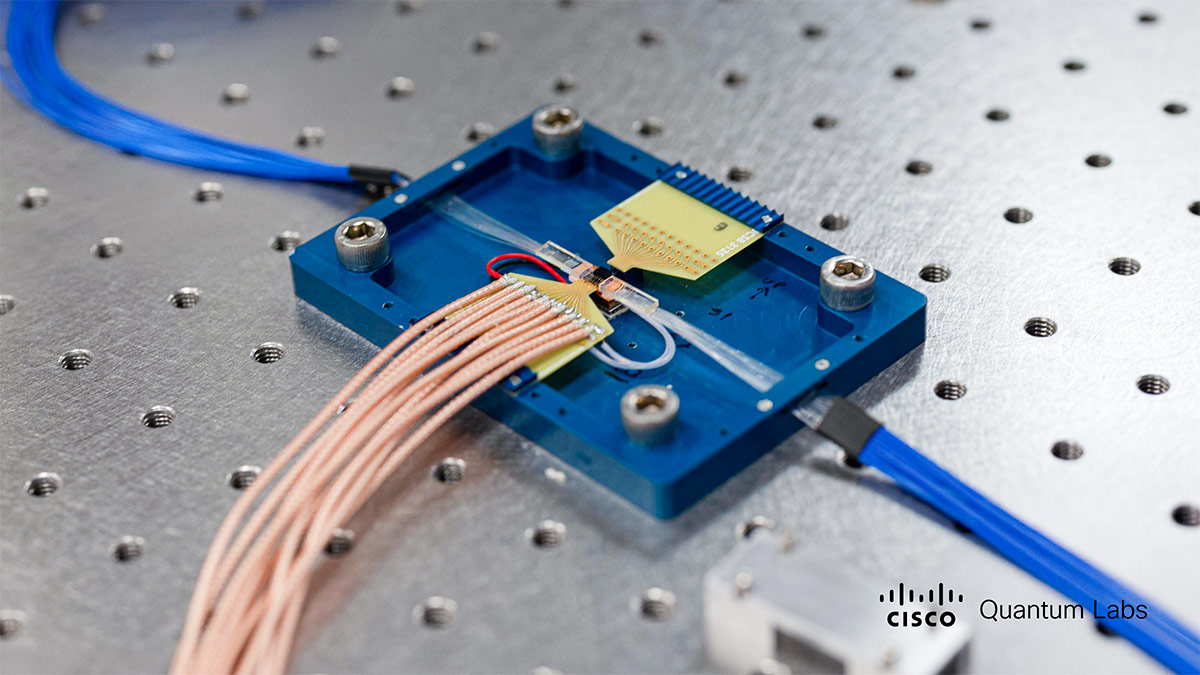
A. Billions of dollars are being invested in quantum computing and we do know there is progress being made in academia and in the private sector. There are private-sector organizations that have made proof-of-concept systems that are very simplistic, but still work.
They are not at a size which is adequate to calculate the prime factors in encryption. What we don’t see is what is being developed in secret. This really is the issue. We know this is something that interests the world’s superpowers greatly.
Of course, if you were to develop a quantum computer which is sizeable and powerful enough to crack encryption, you wouldn’t tell anyone.
We don’t know if such a system is even possible, to be fair, but we need to be prepared for the possibility that such a system could be operational within the coming years.
Q. How can you be sure someone isn’t using a quantum computer to break encryption already?
A. There’s likely to be indications that such a computer is in use. If you were a nation state that possessed such an item, I think you would find it very difficult to resist the temptation to use it, so we would expect to see more evidence of communications systems being intercepted.
When such a system becomes available, I think there will be clues. Given the level of investment going into this, it’s something which is probably on the immediate horizon. It could be tomorrow.
Q. What should security chiefs do to avoid being hacked by a quantum computer?
A. The algorithms that are believed to be ‘quantum insecure’ are those that rely on public key cryptography.
There are candidate algorithms that are believed to be quantum secure—there is currently standardization work being undertaken by the National Institute of Standards and Technology in the United States.
Also, it is expected that keys of greater than 3,072 bits are going to be quantum secure for the foreseeable future, so we have an upgrade pathway. But we need to be developing systems so that we can swap out encryption algorithms as and when necessary.
###